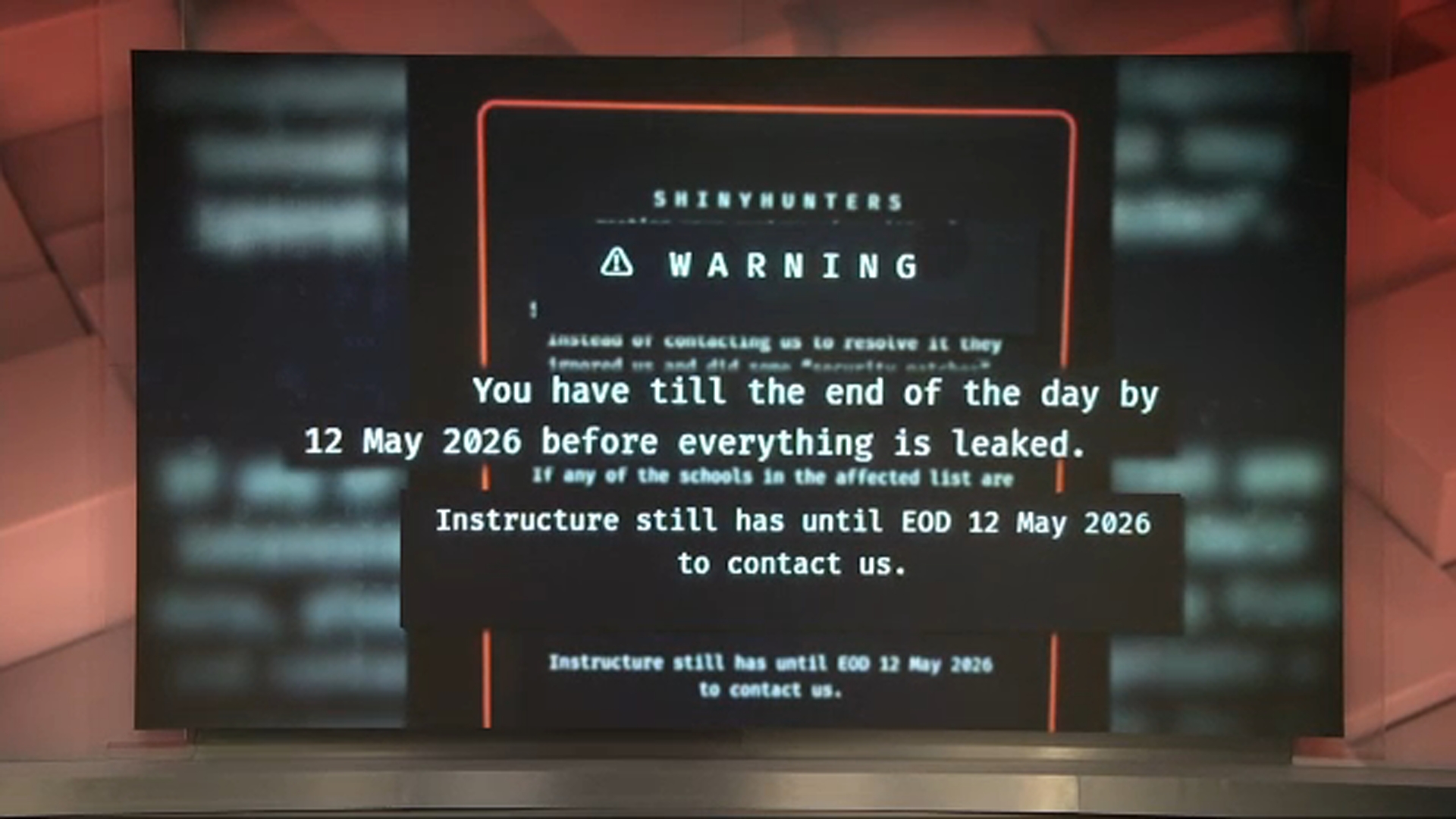
Last week, a cybercriminal group called ShinyHunters hacked Instructure — the company behind Canvas, the learning management platform used by universities and schools worldwide. Instructure confirmed the breach on May 3, 2026, and the numbers are staggering: up to 9,000 institutions affected, with names, email addresses, student ID numbers, and private messages exposed across potentially hundreds of millions of accounts.
If you’ve heard about it, you might be thinking — “that’s a school problem, not a business problem.”
That’s exactly the kind of thinking that gets businesses hacked.
What Actually Happened
ShinyHunters didn’t kick down a door. Instead, they found a vulnerability in Canvas’s cloud environment, registered malicious connected applications inside the platform, and used automated scripts to quietly extract massive amounts of data through legitimate-looking API calls.
No ransomware. No dramatic system shutdown. Just silent, automated data theft — the kind that can go undetected for weeks.
The attackers stole names, email addresses, student ID numbers, and private messages. They confirmed no passwords or financial data were taken — but that information is more than enough to launch targeted phishing attacks against every single person in the database.
This is how modern breaches work. Rather than locking you out of your own systems, attackers simply take what they need and disappear. Often, you find out weeks later when the damage is already done.
Why This Matters for Edmonton Businesses
Canvas is an enterprise SaaS platform used by some of the largest institutions in the world. It has a dedicated security team, significant IT resources, and enterprise-grade infrastructure. Despite all of that, ShinyHunters still got in.
Now think about the average Edmonton SMB — a law firm, a construction company, a healthcare provider, or an accounting office. Most businesses run a combination of cloud platforms: Microsoft 365, QuickBooks Online, a CRM, and maybe a project management tool. Each one of those integrations is a potential entry point. Furthermore, each connected application, each API key, and each third-party tool represents a surface that needs active monitoring and security.
The same techniques ShinyHunters used against Canvas — exploiting cloud integrations, abusing API access, and automating data extraction — target businesses of every size every single day. Attackers don’t only go after universities. They go after whoever has the weakest defences and the most valuable data.
For an Edmonton law firm, that valuable data includes client case files and privileged communications. For a construction company, it means contracts, banking details, and subcontractor agreements. For a healthcare provider, it covers patient records subject to Alberta’s Health Information Act.
The value is there. The question is whether the protection is too.
5 Things This Breach Teaches Every Business
1. Cloud platforms are not automatically secure Using Microsoft 365, Google Workspace, or any other reputable cloud service does not mean your data is protected. In fact, security is a shared responsibility — the platform secures the infrastructure, but your business is responsible for how it’s configured, who has access, and what third-party apps connect to it.
2. Third-party integrations are your biggest blind spot ShinyHunters gained access through a connected application — a third-party integration with API access to Canvas’s data. As a result, most businesses have no idea how many apps connect to their cloud environments or what permissions those apps hold. Every integration you’ve ever authorized is a potential vulnerability if left unmonitored.
3. API access needs to be locked down APIs are how your software systems communicate with each other. They’re essential — and attackers heavily target them. Specifically, unused API keys, over-permissioned applications, and unmonitored API activity are all open doors for automated extraction scripts.
4. Data theft doesn’t always look like an attack The Canvas breach involved no ransomware, no system outage, and no obvious signs of intrusion. Instead, the attackers moved quietly using legitimate-looking tools. Without active monitoring and anomaly detection, this kind of breach goes completely unnoticed until the data shows up for sale on the dark web.
5. Phishing attacks always follow a breach ShinyHunters stole names, emails, and private messages — more than enough to craft highly convincing phishing emails. Similarly, any business breach that exposes employee data, client contact lists, or internal communications will trigger a wave of targeted phishing attempts against everyone affected.
What a Properly Protected Edmonton Business Looks Like
This isn’t about fear — it’s about preparation. Businesses that avoid breaches aren’t lucky; they’re protected. Here’s what proper cybersecurity looks like in practice:
24/7 monitoring — Your security team actively watches your network, endpoints, and cloud environments around the clock. For example, a script suddenly pulling large volumes of data through an API at 2 AM gets flagged immediately, not discovered six weeks later.
Regular access audits — Every connected application, every API key, and every user account with elevated permissions gets reviewed on a schedule. Anything unused, over-permissioned, or unrecognized gets removed immediately.
Multi-factor authentication everywhere — MFA on every account, especially anything with administrative access to cloud platforms, stops a massive percentage of credential-based attacks on its own.
Endpoint detection and response (EDR) — Advanced threat detection runs on every device that touches your network, identifying suspicious behaviour even when no known malware signature exists.
Employee security awareness training — Your team serves as your last line of defence against phishing. Regular training on how to identify suspicious emails, fake login pages, and social engineering attempts dramatically reduces your overall risk.
Incident response planning — When something happens — and eventually something will — a clear, practiced plan helps you contain the breach, notify affected parties, and recover quickly.
The Cost of Not Acting
A single data breach costs Canadian SMBs an average of $3.4 million when you factor in lost business, legal fees, regulatory fines, notification costs, and reputational damage. For a small business, that number is often existential.
Moreover, the Canvas breach is a reminder that no platform, no company, and no industry is immune. Therefore, the question isn’t whether your business will be targeted — it’s whether you’ll be ready when it happens.
GuidePost Can Help
GuidePost Technologies provides cybersecurity services built specifically for Edmonton and Alberta businesses. From 24/7 threat monitoring and endpoint protection to cloud security audits and employee training, we help you build a defence that actually works — before an attack happens, not after.
Explore our Cybersecurity Services →
Or call us directly at 780-851-5000 to book a free cybersecurity assessment for your business.
GuidePost Technologies — Managed IT Services, Cybersecurity, Cloud, and Network Support for Edmonton and Alberta Businesses.